Cloud
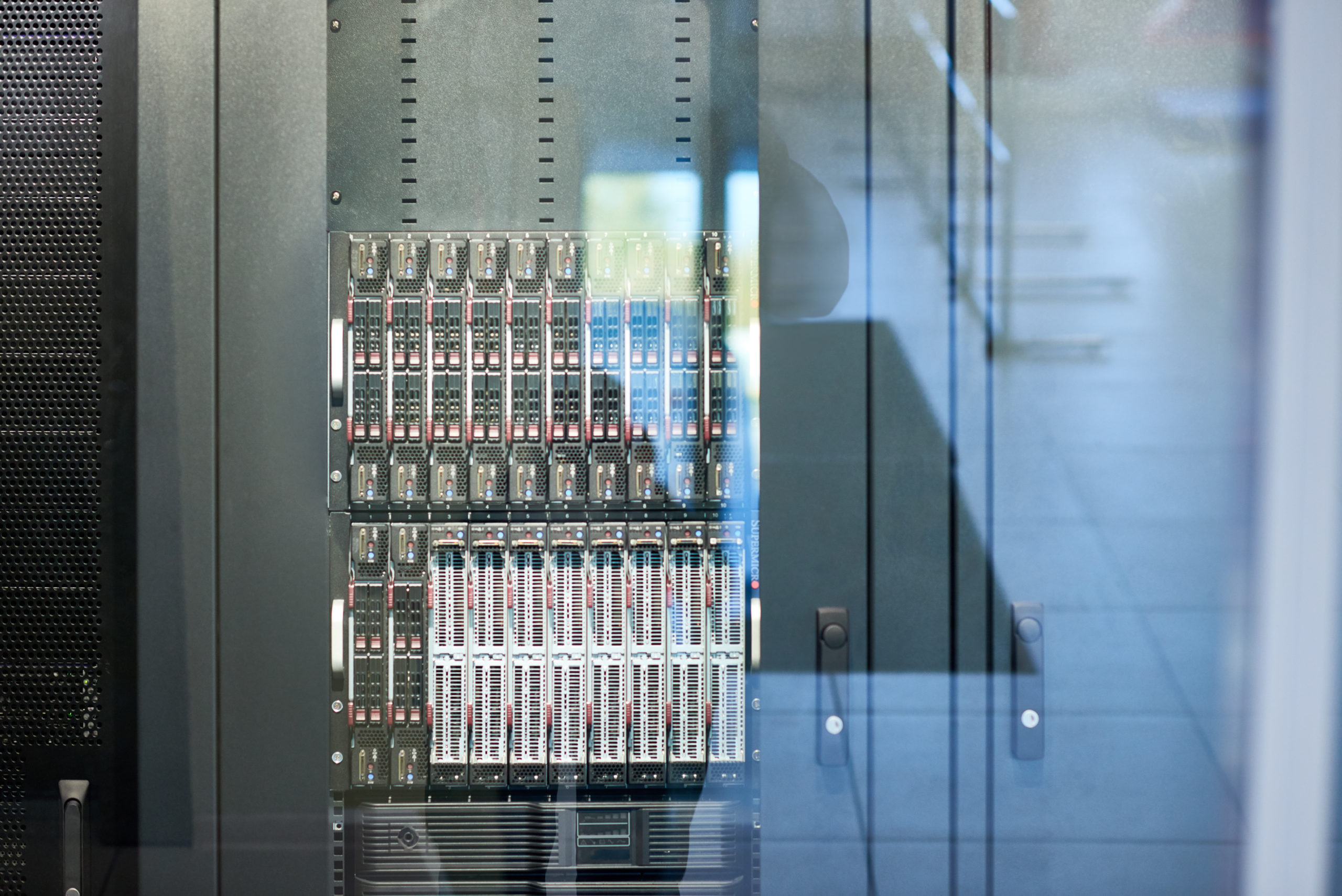
Our world and the way we conduct business has changed rapidly in recent months; and while cloud technology is not exactly new, the rate at which businesses are expected to, and needing to, embrace the cloud is staggering. Team 29B can assist as you migrate to cloud-based computing. We can help you improve productivity and reduce IT expenditures while improving your security posture. Cloud computing can support so many aspects of the IT infrastructure: email, virtual desktops, software development and testing, data backup and disaster recovery… the list goes on. Let us help you harness the power of the Cloud to mobilize your workforce while maintaining the highest security standards required of your industry.
When deployed correctly, cloud resources can provide the availability, scalability and reliability you need, plus the security you demand.
Cloud migration
Whether your organization wants to replace on premise email with Office365/Gsuite or all on premise server infrastructure, our certified engineers have you covered. Our expertise with Azure and VMware cloud offerings can help you optimize performance, increase resiliency, lower costs, and improve security in the cloud.
Cloud-managed IT via CIsco Meraki
Team 29B has helped our customers integrate the leading web-based, centrally managed IT solutions from Cisco Meraki including wireless networking, switching, security, enterprise mobility management (EMM), communications, and security cameras. These cloud-managed solutions enable you to focus on growing your business while providing you IT solutions that are easier to manage than traditional network hardware and software.
BYOD & IoT
Bring Your Own Device (BYOD) and the Internet of Things (IoT) is here to stay. Companies need to evolve their IT methodology to support the ever-changing demands and risks that these two paradigms present. Let Team 29B experts help you embrace BYOD and IoT while maintaining a secure and compliant network. We have an arsenal of security tools that can be quickly deployed across your network to detect and protect against unwelcomed intruders and devices.
Cisco ISE
DUO
Umbrella
Secure Endpoint
A multi-pronged approach to security is needed when it comes to BYOD. Not only do you need to control access, but you need to control the data once it leaves the network. You should consider the following areas when it comes to BYOD:
- Encryption for data at rest and in transit
- Application installation control
- Mobile device management (MDM)
- Policy controls that define what applications/data to allow or deny
Antivirus and anti-malware deployment
